cybersecurity
-
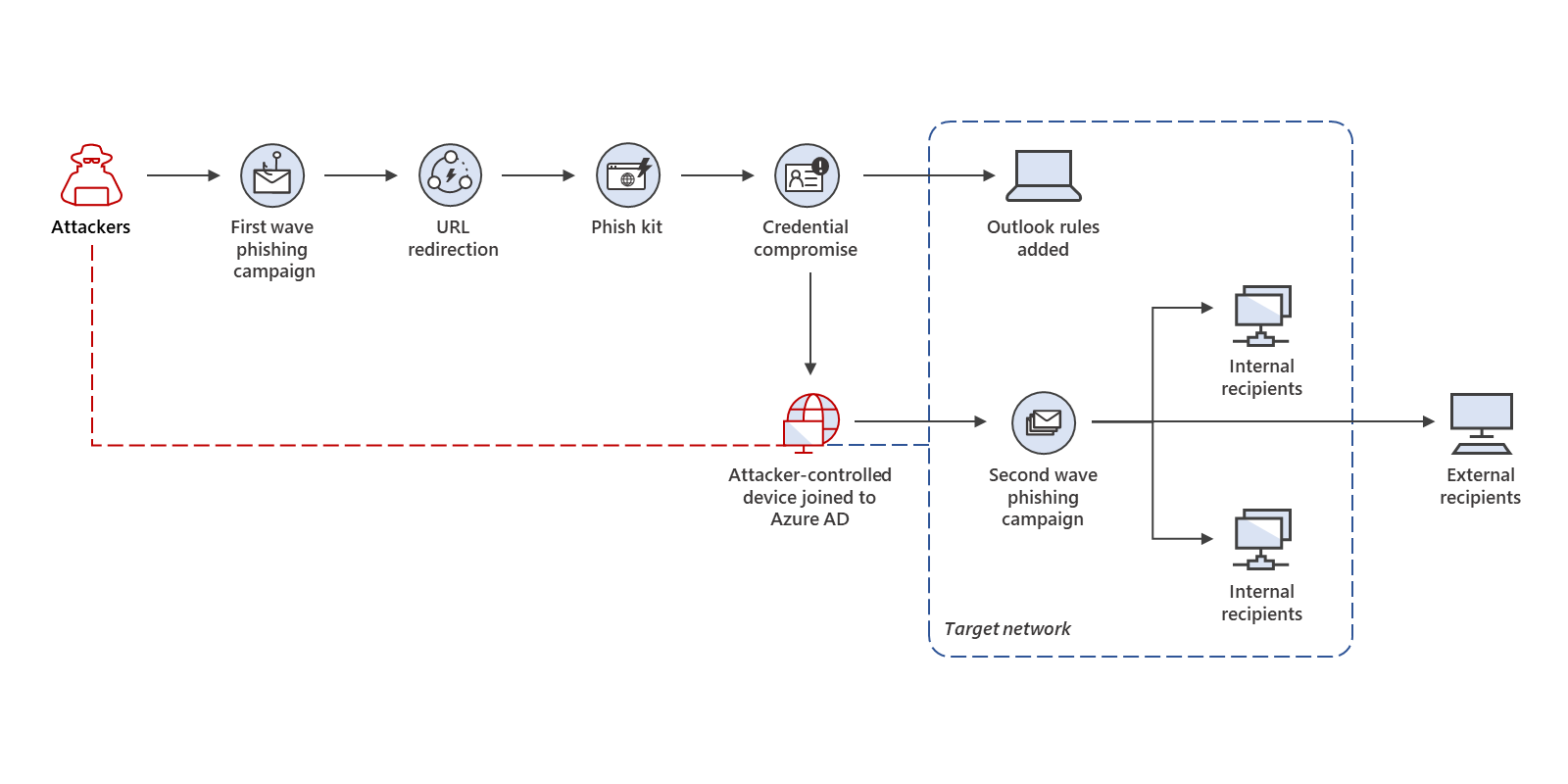
Evolved phishing: Device registration trick adds to phishers’ toolbox for victims without MFA
We have actually just recently revealed a massive, multi-phase project that includes an unique method…
-

Celebrating 20 Years of Trustworthy Computing
20 years ago this week, Bill Gates sent a now-famous email to all Microsoft employees…