Getting a bug has actually taken place to lots of users in some style or another. To most, it is just a moderate hassle, needing a clean-up and after that setting up that anti-virus program that you’’ ve been indicating to set up however never ever navigated to.
However, in other cases, it can be a total catastrophe, with your computer system developing into an extremely costly brick which no quantity of anti-viruses can secure.
In this list, we will highlight a few of the worst and infamous trojan horse that have actually triggered a great deal of damage in reality. And considering that individuals typically relate basic malware like worms and trojan horses as infections, we’’ re including them. These malware have actually triggered significant damage, totaling up to billions of dollars and interrupting crucial reality facilities.
Here are the 10 most harmful and popular trojan horse.
10 Signs Your PC Has Been Compromised .10 Signs Your PC Has Been Compromised.
We are all tired of our PC getting contaminated or jeopardized however fact is in some cases, rather of having … Read more
.1. ILOVEYOU.
ILOVEYOU is thought about among the most virulent trojan horse ever produced. It handled to trash havoc on computer system systems all over the world with around $ 10 billion worth of damages. 10% of the world’’ s computer systems were thought to have actually been contaminated. It was so bad that federal governments and big corporations took their mailing system offline to avoid infection.



The infection was developed by 2 Filipino programers, Reonel Ramones and Onel de Guzman. What it did was usage social engineering to get individuals to click the accessory; in this case, a love confession. The accessory was in fact a script that impersonates a TXT file, due to Windows at the time concealing the real extension of the file.
Once clicked, it will send itself to everybody in the user’’ s sending by mail list and continue to overwrite files with itself, making the computer system unbootable. The 2 were never ever charged, as there were no laws about malware. This caused the enactment of the E-Commerce Law to resolve the issue.
.2. Code Red.
Code Red initially appeared on 2001 and was found by 2 eEye Digital Security workers. It was called Code Red due to the fact that the set were consuming Code Red Mountain Dew at the time of discovery.
The worm targeted computer systems with Microsoft IIS web server set up, making use of a buffer overflow issue in the system. It leaves really little trace on the hard drive as it has the ability to run completely on memory, with a size of 3,569 bytes.
Once contaminated, it will continue to make a hundred copies of itself however due to a bug in the programs, it will replicate a lot more and winds up consuming a great deal of the systems resources.



It will then introduce a rejection of service attack on a number of IP address, popular amongst them was the attack on the White House site . It likewise enables backdoor access to the server, permitting remote access to the device.
The most remarkable sign is the message it leaves on impacted websites, “Hacked By Chinese!”, which has actually ended up being a meme itself. A spot was later on launched and it was price quote that it triggered $2 billion in lost performance. An overall of 1-2 million servers were impacted, which is remarkable when you think about there were 6 million IIS servers at the time.
.3. Melissa.
Named after a stripper from Florida, it was produced by David L. Smith in 1999. It began as a contaminated Word file that was published up on the alt.sex usenet group, declaring to be a list of passwords for adult websites. This got individuals curious and when it was downloaded and opened, it would activate the macro inside and release its payload.
The infection will mail itself to the leading 50 individuals in the user’’ s email address book and this triggered a boost of e-mail traffic, interrupting the e-mail services of corporations and federal governments. It likewise often damaged files by placing a Simpsons referral into them.



Smith was ultimately captured when they traced the Word file to him. The file was submitted utilizing a taken AOL account and with their aid, police had the ability to detain him less than a week considering that the break out started.
He complied with the FBI in recording other infection developers, well-known amongst them the developer of the Anna Kournikova infection. For his cooperation, he served just 20 months and paid a fine of $5000 of his 10 year sentence. The infection supposedly triggered $80 million in damages.
.4. Sasser.
A Windows worm initially found in 2004, it was developed by computer technology trainee Sven Jaschan, who likewise produced the Netsky worm. While the payload itself might be viewed as just irritating (it decreases and crashes the computer system, while making it tough to reset without cutting the power), the impacts were extremely disruptive, with countless computer systems being contaminated, and crucial, crucial facilities impacted.
The worm benefited from a buffer overflow vulnerability in Local Security Authority Subsystem Service (LSASS), which manages the security policy of regional accounts triggering crashes to the computer system. It will likewise utilize the system resources to propagate itself to other makers through the Internet and contaminate others instantly.



The impacts of the infection were extensive as while the make use of was currently covered, lots of computer systems sanctuary ’ t upgraded. This caused more than a million infections , getting crucial facilities, such as airline companies, news companies, public transport, medical facilities, public transportation, and so on. In general, the damage was approximated to have actually cost $18 billion. Jaschen was attempted as a small and got a 21 month suspended sentence.
.5. Zeus.
Zeus is a Trojan horse made to contaminate Windows computer systems so that it will carry out different criminal jobs. The most typical of these jobs are typically man-in-the-browser keylogging and kind grabbing. Most of computer systems were contaminated either through phishing rip-offs or drive-by downloads.
First determined in 2009, it handled to compromise countless FTP accounts and computer systems from big international corporations and banks such as Amazon, Oracle, Bank of America, Cisco, and so on. Controllers of the Zeus botnet utilized it to take the login qualifications of social media network, e-mail and banking accounts.



In the United States alone, it was approximated that more than 1 million computer systems were contaminated, with 25% in the United States. The whole operation was advanced, including individuals from worldwide to serve as cash mules to move and smuggle money to the ringleaders in Eastern Europe.
.
About$ 70 million were taken and in belongings of the ring. 100 individuals were apprehended in connection of the operation. In late 2010, the developer of Zeus revealed his retirement however lots of specialists think this to be incorrect.
.6. Conficker.
Also referred to as Downup or Downadup, Conficker is a worm of unidentified authorship for Windows that made its very first look in 2008. The name comes form the English word, configure and a German pejorative. It contaminates computer systems utilizing defects in the OS to produce a botnet.
The malware had the ability to contaminate more than 9 millions computer systems all around the world, impacting federal governments, people and organizations. It was among the biggest recognized worm infections to ever appear triggering an quote damage of $9 billion.
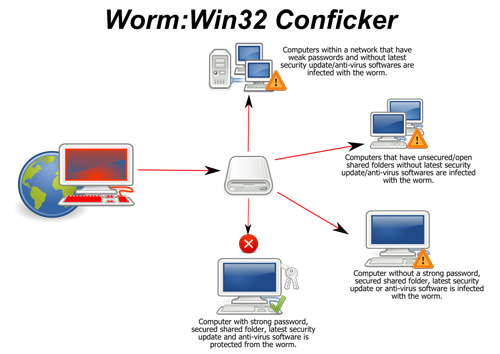
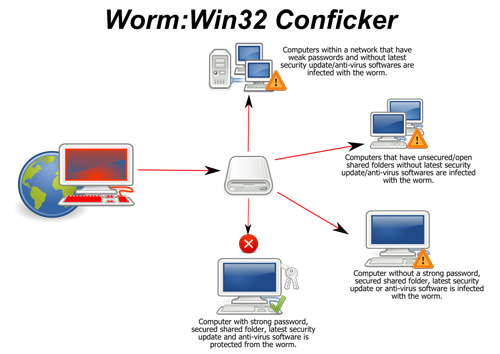
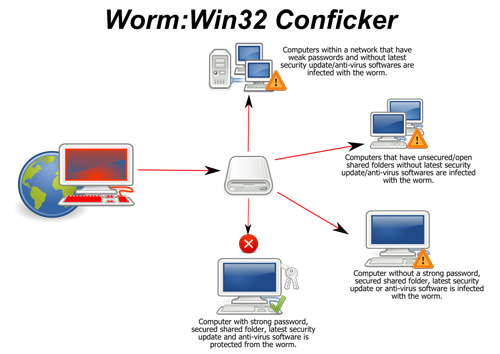
The worm works by making use of a network service vulnerability that was unpatched and present in Windows. When contaminated, the worm will then reset account lockout policies, obstruct access to Windows upgrade and anti-viruses websites, switch off specific services and lock out user accounts amongst numerous.
Then, it continues to set up software application that will turn the computer system into a botnet servant and scareware to fraud cash off the user. Microsoft later on supplied a repair and spot with lots of anti-viruses suppliers offering updates to their meanings.
.7. Stuxnet.
Believed to have actually been produced by the Israeli Defence Force together with the American Government, Stuxnet is an example of an infection developed for the function of cyberwarfare, as it was meant to interfere with the nuclear efforts of the Iranians. It was approximated that Stuxnet handled to destroy one 5th of Iran’’ s nuclear centrifuges which almost 60% of infections were focused in Iran.
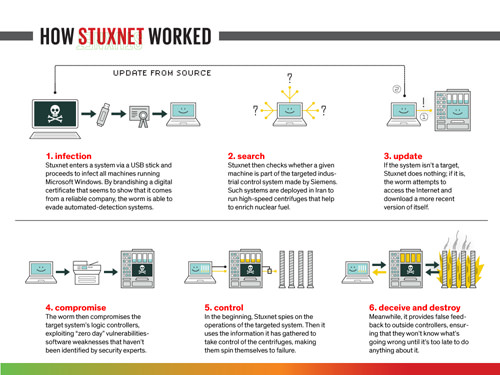
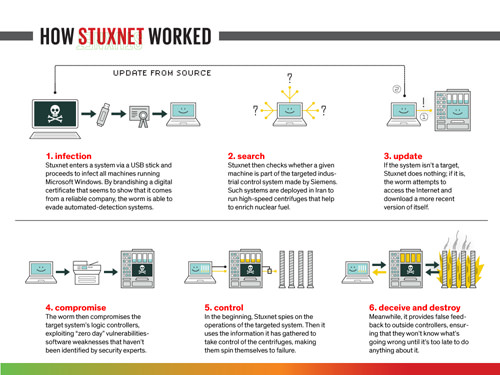
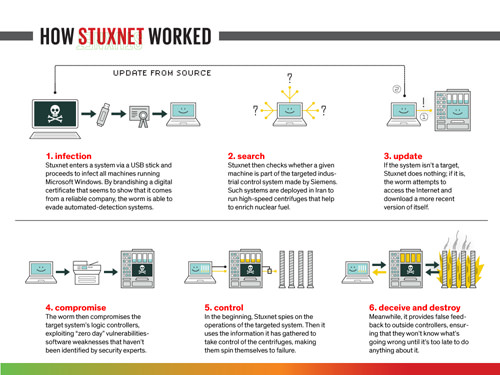
The computer system worm was created to assault commercial Programmable Logic Controllers (PLC), which permits automation of procedures in equipment.
It particularly focused on those developed by Siemens and was spread out through contaminated USB drives. It changed the speed of the equipment, triggering it to tear apart. If the contaminated computer system didn’’ t include Siemens software application, it would lay inactive and contaminate others in a minimal style regarding not offer itself away. Siemens ultimately discovered a method to eliminate the malware from their software application.
.8. Mydoom.
Surfacing in 2004, Mydoom was a worm for Windows that turned into one of the fastest spreading out e-mail worm because ILOVEYOU. The author is unidentified and it is thought that the developer was paid to produce it considering that it includes the text, ““ andy; I ’ m simply doing my task, absolutely nothing individual, sorry,””.
.
It was called by McAfee worker Craig Schmugar, among individuals who had actually initially found it. ‘‘ mydom ’ was a line of text in the program’’ s code( my domain) and noticing this was going to be huge, included ‘‘ doom ’ into it.


The worm spreads itself by looking like an e-mail transmission mistake and includes an accessory of itself. As soon as performed, it will send itself to email addresses that remain in a user’’ s deal with book and copies itself to any P2P program’’ s folder to propagate itself through that network.
The payload itself is twofold: initially it opens a backdoor to permit remote gain access to and 2nd it releases a rejection of service attack on the questionable SCO Group. It was thought that the worm was developed to interrupt SCO due to contrast over ownership of some Linux code. It triggered an quote of $38.5 billion in damages and the worm is still active in some type today.
.9. CryptoLocker.
CryptoLocker is a kind of Trojan horse ransomware targeted at computer systems running Windows. It utilizes a number of techniques to spread itself, such as e-mail, and when a computer system is contaminated, it will continue to secure specific files on the hard disk and any installed storage linked to it with RSA public crucial cryptography.
While it is simple enough to eliminate the malware from the computer system, the files will still stay encrypted. The only method to open the files is to pay a ransom by a due date. The ransom will increase substantially or the decryption secrets erased if the due date is not fulfilled. The ransom typically total up to $400 in pre-paid money or bitcoin.



The ransom operation was ultimately stopped when police and security business handled to take control part of the botnet running CryptoLocker and Zeus.
Evgeniy Bogachev, the ring leader, was charged and the file encryption secrets were launched to the impacted computer systems. From information gathered from the raid, the variety of infections is approximated to be 500,000, with the variety of those who paid the ransom to be at 1.3%, totaling up to $3 million.
.10. Flashback.
Though not as destructive as the remainder of the malware on this list, this is among the couple of Mac malware to have gain prestige as it revealed that Macs are not immune. The Trojan was very first found in 2011 by anti-viruses business Intego as a phony Flash set up.
In its more recent version, a user just requires to have Java allowed (which is most likely most of us). It propagates itself by utilizing jeopardized sites consisting of JavaScript code that will download the payload. When set up, the Mac enters into a botnet of other contaminated Macs.



The great news is that if it is contaminated, it is merely localized to that particular user ’ s account. The problem is that more than 600,000 Macs were contaminated, consisting of 274 Macs in the Cupertino location, the head office of Apple.
.
Oracle released a repair for the make use of with Apple launching an upgrade to eliminate Flashback from individuals ’ s Mac. It is still out in the wild, with an quote of 22,000 Macs still contaminated since 2014.
.
The post 10 Deadliest Computer Viruses of All Time appeared initially on Hongkiat .
Read more: hongkiat.com