
The finals of the Pwn2Own ethical hacking battle are finally over with the last events conducted on 08th April. The results were divided among 50% complete success and the remaining 50% were partial wins. The event started in a great manner at 0900 in the morning when Benjamin McBride won $40000 for executing code on host OS from within Parallels desktop.
 Image: Zeroday Initiative
Image: Zeroday Initiative
The next set of four events towards Microsoft Exchange, Ubuntu desktop, Windows 10, and Parallels Desktop were termed as a partial success because of all the methods used in these four events and the bug reported was already known by the respective organizations. There were no cash prizes awarded here but the winners were given points towards Master of PWN. The main highlight of these events was Alisa Esage, the first woman to participate as an independent researcher, and targeted Parallels Desktop in the Virtualization category.
 Image Courtesy: Twitter
Image Courtesy: Twitter
The final three events towards Ubuntu Desktop, Parallels Desktop and Windows 10 desktop all resulted in success and were awarded cash prizes. Vincent Dehors claimed $30,000 to escalate to the root of the Ubuntu desktop through a double-free bug. The next prize of $40,000 was claimed by Da Lao who completed guest to host via OOB Write in Parallels Desktop. The final win of the day and the tournament was achieved by Marcin Wiazowski who won a whopping amount of $40,000 after using a UAF bug to gain System Access on a Windows 10 PC.
The entire event was sponsored by VMware and other partners included Adobe, Zoom, and Tesla. The vendors of the event have 90 days to produce a fix for the vulnerabilities reported. Here is a summary report of all three days in case you missed it.
Sn No
Date
Time
Event
Person/Team
Status
1
Apr 6, 2021
1000
Apple Safari
Jack Dates
Success
2
Apr 6, 2021
1130
Microsoft Exchange
DEVCORE
Success
3
Apr 6, 2021
1300
Microsoft Teams
OV
Success
4
Apr 6, 2021
1430
Windows 10
Viettel
Success
5
Apr 6, 2021
1530
Parallels Desktop
Star Labs
Failure
6
Apr 6, 2021
1630
Ubuntu Desktop
Ryota Shiga
Success
7
Apr 6, 2021
1730
Oracle Virtualbox
Star Labs
Failure
8
Apr 7, 2021
0900
Parallels Desktop
Jack Dates
Success
9
Apr 7, 2021
1000
Google Chrome & Microsoft Edge
Bruno Keith & Niklas BaumStark
Success
10
Apr 7, 2021
1130
Microsoft Exchange
Viettel
Partial
11
Apr 7, 2021
1300
Zoom Messenger
Daan Keuper & Thijs Alkemade
Success
12
Apr 7, 2021
1430
Windows 10
Tao Yan
Success
13
Apr 7, 2021
1530
Parallels Desktop
Sunjoo Park
Success
14
Apr 7, 2021
1630
Ubuntu Desktop
Manfred Paul
Success
15
Apr 7, 2021
1730
Windows 10
z3r09
Success
16
Apr 8, 2021
0900
Parallels Desktop
Benjamin McBride
Success
17
Apr 8, 2021
1000
Microsoft Exchange
Steven Seeley
Partial
18
Apr 8, 2021
1130
Ubuntu Desktop
Star Labs
Partial
19
Apr 8, 2021
1230
Windows 10
Fabien Perigaud
Partial
20
Apr 8, 2021
1330
Parallels Desktop
Alisa Esage
Partial
21
Apr 8, 2021
1430
Ubuntu Desktop
Vincent Dehors
Success
22
Apr 8, 2021
1530
Parallels Desktop
Da Lao
Success
23
Apr 8, 2021
1630
Windows 10
Marcin Wiazowski
Success
One glance at the table above would tell you that out of the 23 events scheduled, only 2 failed as the team was not able to complete the task in the allotted time and with 5 Partials, 16 events were a complete success. The 5 partial successes were so-called because the method or bug used was already known before the contest.
For complete results and more details, click here
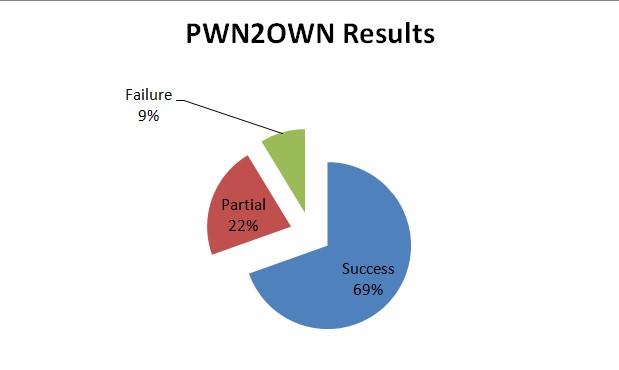
The reason for concern here is if you count the actual total number of successes then it amounts to 21 out of 23 which amounts to 91% success (including partial wins). This brings a serious thought to our mind “Are the operating systems and software we use so vulnerable by hackers?” I leave you to think and ponder over this and please share your comments in the section below.
The post PWN2OWN 2021 Final Results: A Remarkable 90% Of Hacking Attempts Were Successful appeared first on We The Geek.
Read more: wethegeek.com
